Introduction: How “Traditional SSO” became an Attack Surface?
Single Sign-On (SSO) was introduced to reduce operational friction, not to fundamentally change the security model of authentication. Over time, however, SSO systems have evolved into high-value aggregation points for identity, credentials, and authorization context. This evolution has unintentionally transformed SSO itself into a primary attack surface.
From a threat-modeling perspective, modern SSO systems introduce centralization, reuse, and implicit trust expansion – three properties that attackers systematically exploit.
Key reasons traditional SSO became an attack surface:
- Credential and token aggregation
A single successful compromise often yields access to multiple applications.
This violates the principle of minimizing blast radius. - Token replay as a first-class attack primitive
Modern attacks increasingly target session tokens (SAML, OAuth), not passwords.
Once stolen (via phishing, AiTM, or endpoint compromise), tokens are reusable until expiration (T1550.001).
- Adversary-in-the-Middle (AiTM) attacks
Reverse-proxy phishing frameworks (e.g., real-time credential and token harvesting) defeat MFA by relaying authentication flows transparently (T1557).
SSO does not prevent this class of attack; it amplifies its impact. - Centralized identity = centralized failure (T1072)
SSO systems were designed to make authentication easier, not to make credentials non-exploitable.
The core problem is that most SSO implementations still rely on reusable secrets (passwords, tokens), federation trust, or externally issued assertions. These assumptions were reasonable in a pre-AiTM, pre-cloud, pre-SaaS-sprawl threat landscape. They are increasingly fragile today.
Mapping to MITRE ATT&CK
- T1566 – Phishing for initial access
- T1557 – Adversary-in-The-Middle
- T1555.005 – Credential from Password Stores (Password Managers)
- T1078.004 – Valid Accounts (Cloud Accounts)
- T1550.001 – Use Alternate Authentication Material (Application Access Token)
Threat Model and Real-World Attacks Analysis
This analysis focuses on identity-centric attacks that exploit authentication material, trust relationships, and federation.
In-scope threats
- Credential theft – Phishing, OAuth consent abuse, and AI-assisted social engineering
- AiTM – Real-time interception and replay of authentication flows
- Session token compromise – Theft and reuse of OAuth/OIDC tokens and cookies
- Identity-based lateral movement – Pivoting across SaaS applications using valid identity context
- Federated trust abuse – Exploiting centralized IdP trust relationships
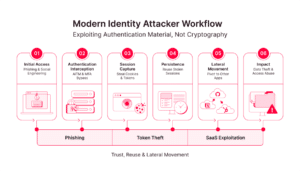
Modern Identity Attacker Workflow
Most successful identity breaches follow a predictable sequence that targets authentication material, not cryptography. The attacker never breaks cryptography – they abuse trust and reuse.
Real World Attacks that Exploit These Patterns
AiTM – Microsoft Phishing Campaigns (2022 – present)
Since 2022, Microsoft has documented multiple Adversary-in-the-Middle (AiTM) phishing campaigns targeting Microsoft 365 tenants. These attacks did not rely on password cracking or MFA bypass, but on real-time interception and replay of authentication sessions.
Attack summary [credit to this Microsoft blog]
In these Microsoft 365 AiTM campaigns, attackers abused trusted SharePoint document-sharing workflows to deliver highly credible phishing lures, causing victims to complete authentication and MFA legitimately. A reverse-proxy AiTM infrastructure relayed the real login flow in real time, allowing attackers to capture session cookies and OAuth tokens after successful authentication. With valid session material, the attackers established persistence by creating malicious mailbox rules to hide activity and suppress user awareness, then leveraged the compromised identities to conduct large-scale intra-organizational phishing and business email compromise (BEC), significantly expanding the impact across the tenant.
Why SSO and MFA failed:
- MFA protects authentication, not session reuse
- Session cookies function as bearer credentials
- Federation allowed one successful login to unlock multiple services
Lateral Movement – Golden SAML & Seamless SSO
The most damaging aspect of modern identity attacks is not initial access, but lateral movement enabled by identity reuse and federation. Attacks such as Golden SAML and Seamless SSO (Kerberos ticket forging) compromise authentication trust at its root, allowing attackers to mint valid authentication material that is automatically accepted across multiple applications.

Why lateral movement succeeds in traditional SSO
- Federated trust allows one authentication event to unlock many applications
- SAML assertions and Kerberos tickets are reusable bearer artifacts
- Applications implicitly trust IdP-issued tokens without additional containment
SolarWinds (2020) and Okta (2023) breaches illustrate the same architectural risk at different layers: when trust is federated, compromise of a single authority becomes compromise of every dependent system. Unixi’s model addresses this failure mode in the identity layer by eliminating transitive authentication trust.
Conclusion
Traditional SSO architectures optimized for convenience have unintentionally concentrated risk by centralizing trust, reusing authentication material, and allowing identity to propagate implicitly across systems. Modern attacks, from AiTM phishing to federation abuse – exploit these properties rather than weaknesses in cryptography itself. As a result, authentication success has become decoupled from security, and compromise increasingly scales laterally through identity.
Unixi addresses this failure mode by redesigning authentication around localization and containment. Through key-derived, system-specific authentication that is never stored or reused, it removes offline attack surfaces, limits replay, and breaks transitive trust. The result is not the elimination of all compromise, but a fundamental reduction in blast radius: authentication failures remain localized, non-reusable, and operationally constrained by design rather than policy.